Getting Credentials from Unprotected Jenkins
Jenkins is a Continuous Integration server. Continuous Integration is the practice of running tests on a non-developer machine automatically every time someone pushes new code into the source repository.
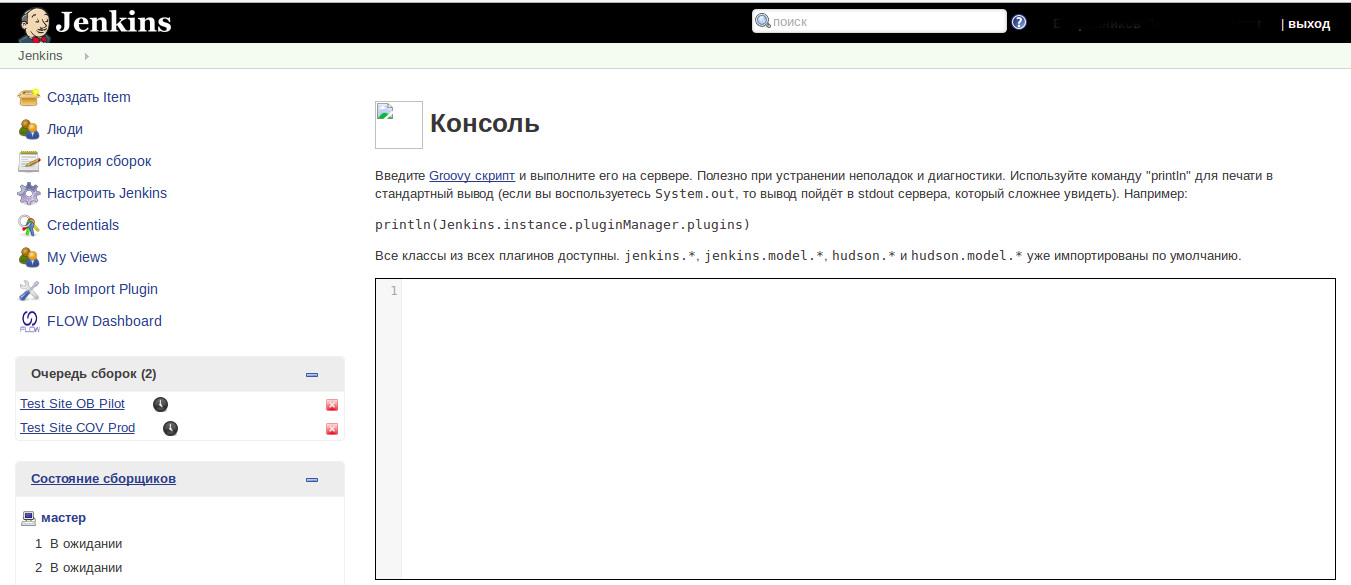
Sometimes you can find Jenkins that is not password protected. This is dangerous because Jenkin instances have /script endpoing. This endpoint contains a textbox where you can paste a Groovy script. Groovy is a kind of a scripting language for Java.
Using the following Groovy code, you can get a list of files in / directory:
def sout = new StringBuffer(), serr = new StringBuffer()
def proc = 'ls'.execute()
proc.consumeProcessOutput(sout, serr)
proc.waitForOrKill(1000)
println "$sout"You can read /etc/passwd to find jenkins home directory. In most cases it is /var/lib/jenkins/.
There are 3 important files in Jenkins:
├── credentials.xml
├── secret.key
├── secret.key.not-so-secret
├── secrets
│ ├── hudson.util.Secret
│ └── master.key
...Jenkins stores user credentials in credentials.xml encrypted. File master.key is used to encrypt hudson.util.Secret key, which in turn encrypts passwords in credentials.xml. Read about how it works here.
You can use /userContent endpoint to get these files from the server. This endpoint in linked to /var/lib/jenkins/. For decryption, use this script.